If you’re still using @Microsoft ‘s on-premise MFA Server, it’s time to move up to Azure MFA with enhanced security and reduced TCO. The latest MFA migration utility makes it easier. Read about it here. ? Tell us if you’d like a demo.
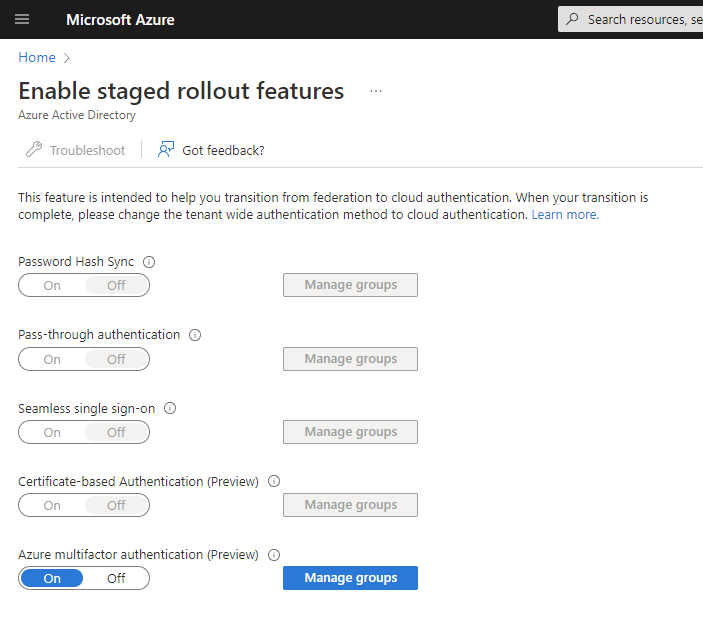
If you’re still using @Microsoft ‘s on-premise MFA Server, it’s time to move up to Azure MFA with enhanced security and reduced TCO. The latest MFA migration utility makes it easier. Read about it here. ? Tell us if you’d like a demo.

Operational excellence isn’t just about increasing efficiencies or ROI — it’s about creating a roadmap for continuous improvement in today’s complex business environment. Learn how automation can help achieve operational excellence in this blog. #OperationalExcellence #Automation

Microsoft is revolutionizing how sales teams sell to and engage prospects with ground-breaking AI-powered experiences. Intrigued? Read this blog to learn about a new generative GPT seller experience in @Microsoft Viva Sales.

Is your business prepared for environmental compliance? The SEC recently proposed to standardize how organizations make climate-related disclosures. The proposed rule would require US publicly traded companies to disclose how they’re assessing, measuring and managing climate-related risks. Read the @IBM article to learn more.

When was the last time you revisited your data strategy? Share this post to start a conversation. Technology evolves quickly, and machine learning and AI allow you to get more valuable insights from your data. Don’t miss out – read this @IBM blog for 5 recommendations to get your data strategy right. #AI #datastrategy

Is your organization looking for ways to power your day-to-day employee experiences? Load testing is helping @Microsoft gain insight into the IoT sensor data it collects to significantly improve employee workplace experiences. DM us to discuss next steps. #MSIoT

Employee well-being and connectedness. Supply chain problems. Changing financial models. Forrester says these 3 forces are driving companies to service-centric business models & project-based operations. What’s driving yours?

When Forrester named the Red Hat Ansible Automation Platform a leader in infrastructure automation, we thought that great news. Its availability on @AWS makes it even better! Learn what sets Ansible apart in this article ? @Red Hat
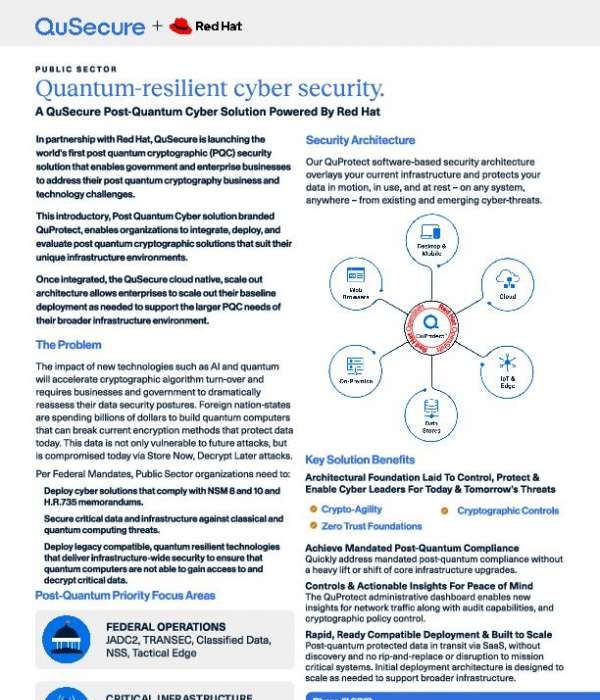
What are the biggest cyber-risks you face in your post-quantum, public sector environment? ✅Dated, asymmetric key exchange algorithms ✅ Exploitable pre-quantum devices ✅ Cryptographic blindness With standards-based and compliant quantum-grade security from QuSecure and Red Hat, BryTech Inc. can help you address all of the above and more. Download this solution brief for an overview of QuProtect.TM @Red Hat @QuSecure

Garner reports 95% of supply chains must quickly react to changing conditions, but only 7% are able to execute decisions in real time. What does this spell for the supply chain future? Share your predictions in the comments. Read the blog to hear what @Gartner has to say ?